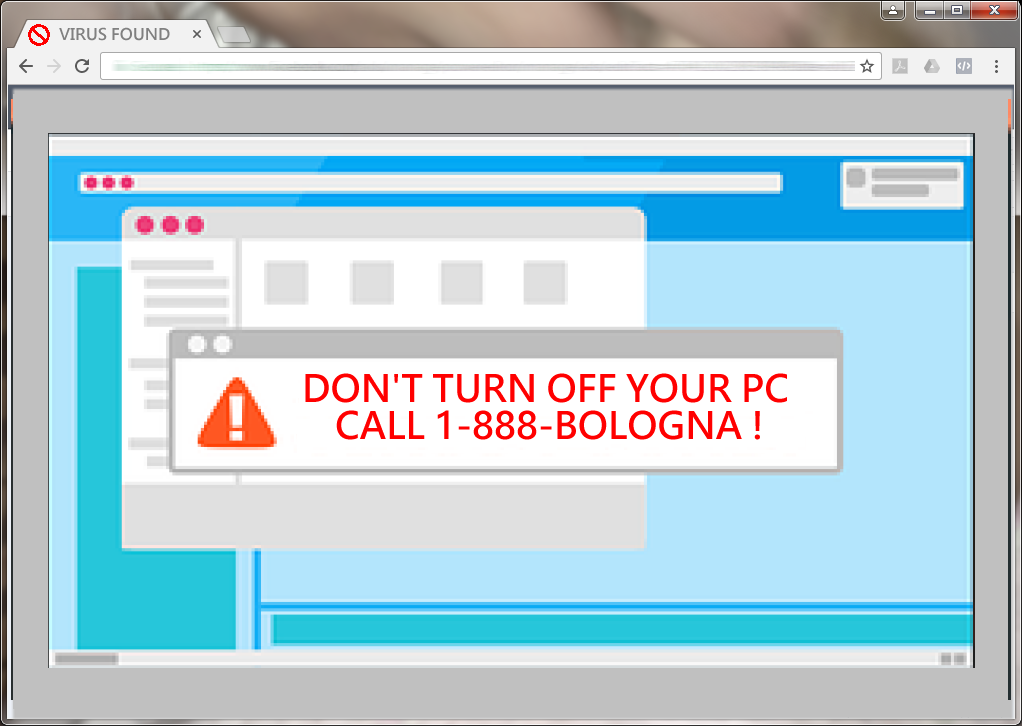
I wrote this short tutorial because I am angry that Overseas Tech Support Shops are using unethical business practices to drum up business. Instead of providing value to their customers and building a relationship of trust first then asking for a value added transaction, they resort to taking them hostage and extort money from them.
Category Archives: Internet Security
Firewall Explained
A firewall is necessary to keep you safe on the internet. But what the heck is it and how does it work? Well, if you have known me for any length of time, you would know that I like to explain things in easy to understand analogies. Most likely I have explained something to you …
Two Tweaks To Avoid Email Scams
The Internet and Email are the most dangerous avenues for viruses and scams. I am going to show you a couple of ways to protect yourself from these threats via email. The first one, is to hide the message reading pane; and the second one is to use the “to” column to verify the recipient …
Do you want to make $$$ with your computer: I can show you how!
All you need is a strong desire and a personal computer. You can use a laptop or even an old typewriter.
OpenSSL what is it and why should you care?
OpenSSL is an encryption method used by websites to provide security against prying eyes. The problem is that someone found a flaw in the programming of a certain kind of SSL. The flaw allows crooks to peer into the working areas of the encryption process and extract important information from it, such as passwords, or …
Continue reading “OpenSSL what is it and why should you care?”